1 Why authorization matters: Securing access in a digital world
Authorization sits at the heart of secure and usable digital systems. The chapter opens with the 2013 Target breach to illustrate how weak authorization boundaries—distinct from authentication—can turn a minor compromise into a major incident. Beyond security, authorization enables core product capabilities in modern cloud applications: sharing and collaboration in services like document platforms, multi-tenant isolation and control in hyperscale clouds, and fine-grained feature access. Framed within digital identity’s purpose to recognize, remember, and relate entities, the chapter positions authorization as the mechanism that determines “what” an authenticated principal may do, and argues it must be treated as an architectural concern rather than ad hoc code.
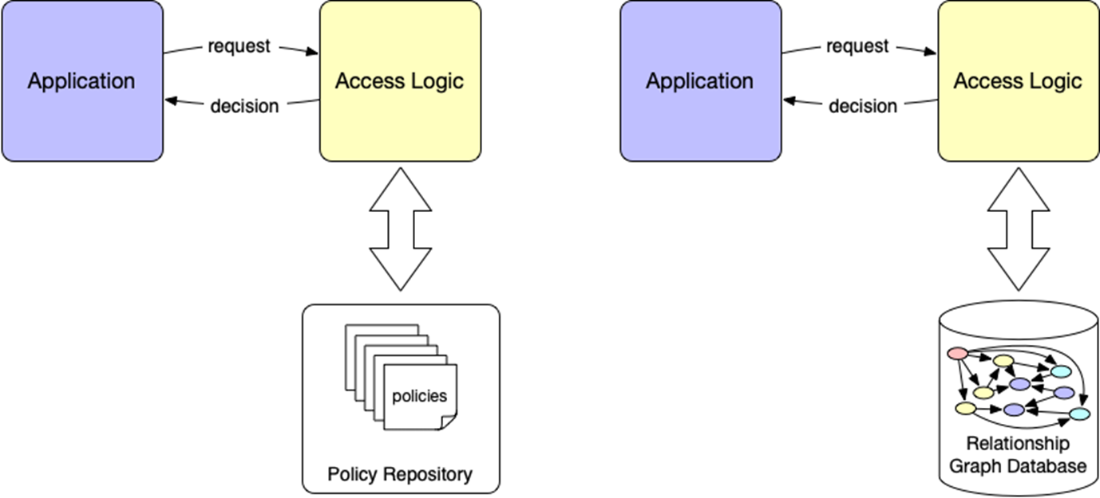
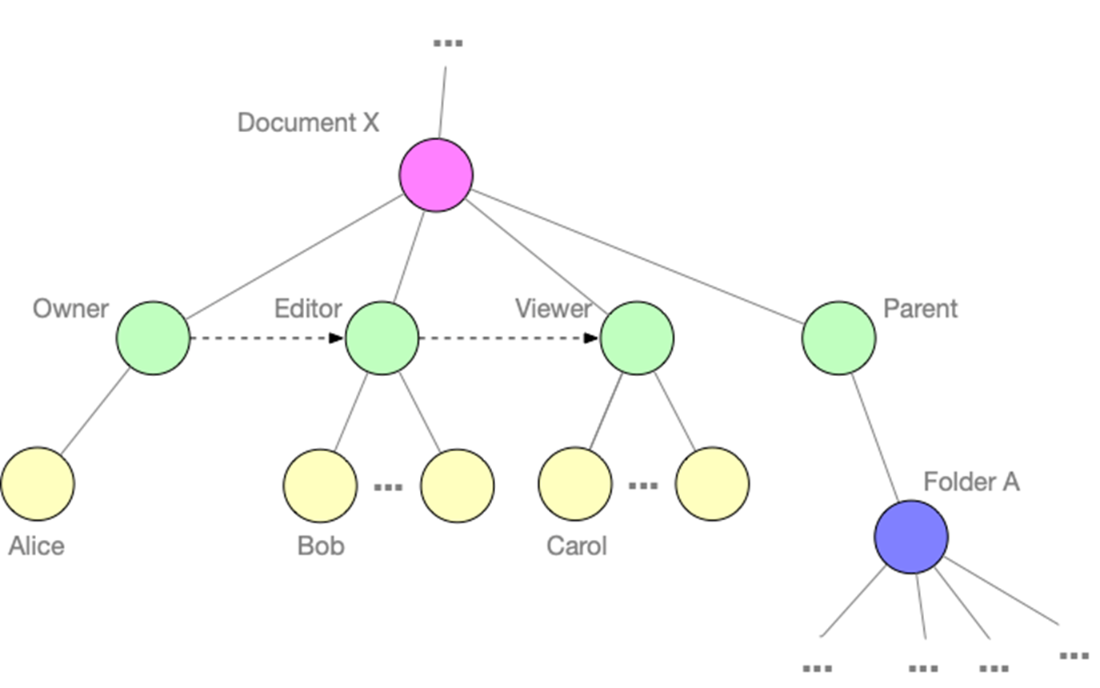
Traditional static methods—permissions, groups, roles, and ACLs—struggle with scale, context, and change: they are hard to maintain, inflexible in dynamic scenarios, opaque to audit, and prone to over-permissioning. Dynamic, policy-based authorization (PBAC) addresses these gaps by externalizing access logic, enabling consistent, fine-grained, context-aware decisions at runtime and supporting zero trust practices. The chapter introduces two complementary representations: Policy as Code (machine-readable, testable, and versioned rules evaluated by a general-purpose engine) and Policy as Data (structured relationships and attributes, such as ownership and sharing graphs, evaluated dynamically). Used together, they combine broad, reusable rules with rich, evolving relationship data to deliver scalable, auditable control across SaaS, IoT, regulated workloads, and AI-assisted applications.
Treating authorization as a first-class architectural element yields tangible business outcomes. Dynamic authorization reduces operational costs (fewer manual changes, cleaner onboarding/offboarding, lower support burden), improves agility (rapid policy changes instead of code rewrites), enhances customer experience (personalized, delegated, and tiered access), and strengthens security and compliance (least privilege, continuous evaluation, and clearer auditability). The chapter concludes by framing dynamic authorization as a strategic imperative for multi-tenant, distributed, and AI-enabled systems, previewing the book’s exploration of models, languages, enforcement patterns, and governance needed to build flexible, testable, and business-aligned authorization at scale.
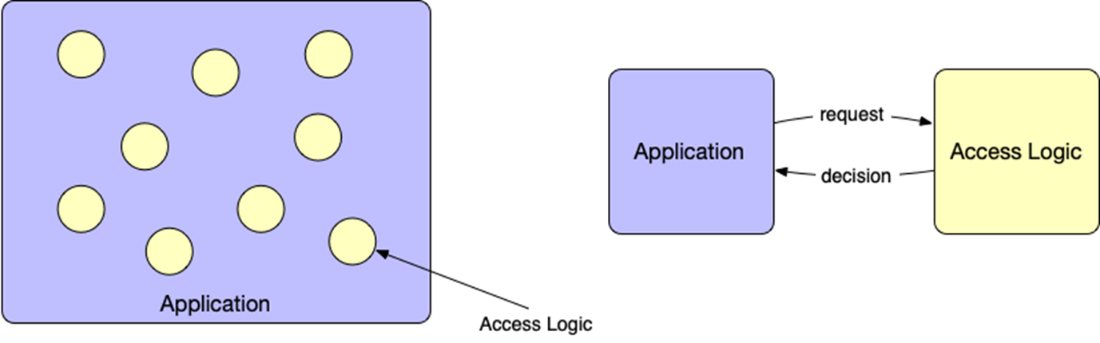
Embedding access logic throughout application code (left) creates tight coupling. Externalizing authorization into a separate component (right) makes access policies explicit, decouples decision-making from application behavior, and enables scalable, auditable access control.
Dynamic authorization can represent policy in two complementary ways. On the left, Policy as Code stores machine-readable policies in a repository that the access logic evaluates at runtime. On the right, Policy as Data stores relationships and attributes in a structured data store that the same access logic uses to determine decisions. Both approaches externalize policy from the application while supporting different kinds of flexibility.
A relationship graph representing access to a Google document. Rather than use static ACLs, this model captures roles (like Owner, Editor, Viewer) as first-class relationships between users and resources. The graph also models hierarchical relationships (such as parent folders), enabling more flexible, general-purpose authorization logic that can be queried and evaluated dynamically.
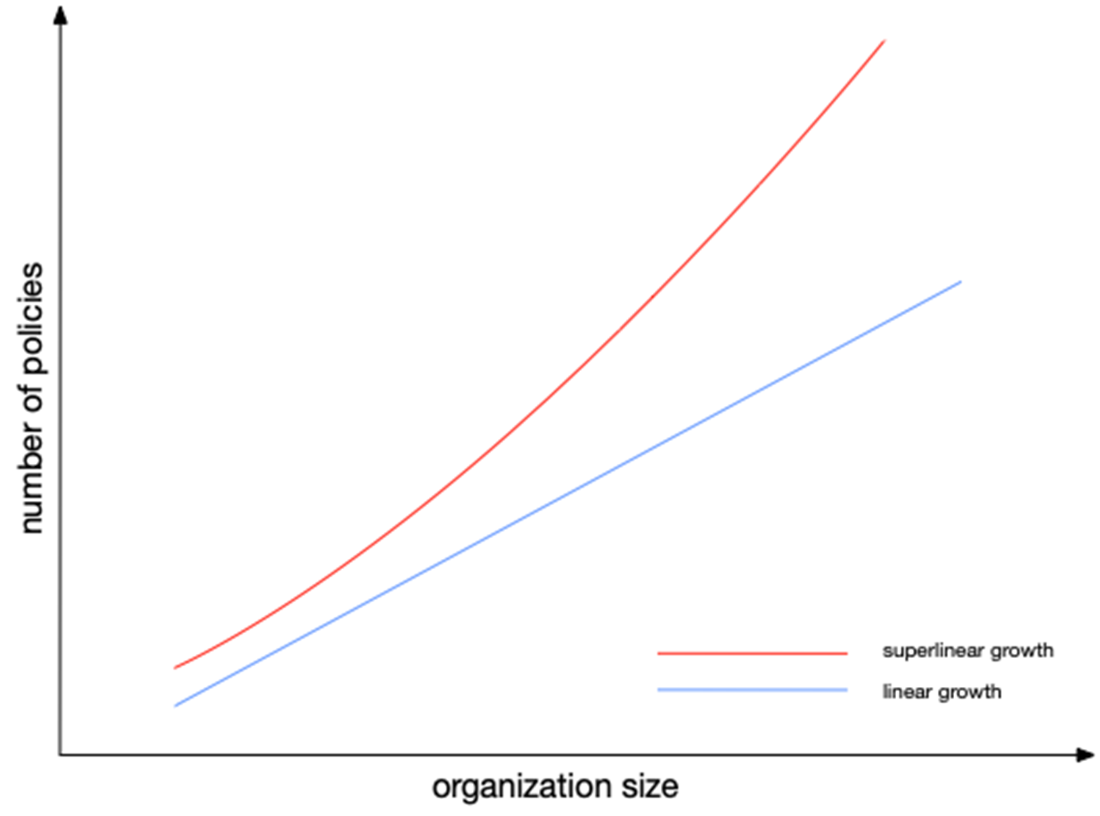
As an organization grows, the number of access policies tends to increase faster than linearly. Though a small organization might manage with a simple, flat set of policies, larger organizations face compounding complexity due to team structures, regional compliance, and overlapping responsibilities, leading to superlinear policy growth.
Summary
- Poor access control can lead to severe security breaches, as seen in the Target breach, where attackers exploited weak authorization to access sensitive systems.
- Authorization is not just about security; it also enables key features in modern cloud applications, such as document sharing and multi-tenant access control.
- Traditional authorization methods like ACLs and RBAC are static and struggle with scalability, flexibility, maintainability, efficiency, auditability, and security.
- Dynamic authorization overcomes these challenges by using policies to make real-time, context-aware access decisions.
- Policy-based access control (PBAC) enables fine-grained authorization by externalizing access control logic, making it dynamic and adaptable to changing conditions.
- The shift toward zero-trust security models, SaaS applications, IoT, regulatory compliance, and AI-driven applications demands more flexible and scalable access control, making dynamic authorization essential.
- Policies can be represented as code or data, enabling both structured rule enforcement and flexible, real-time access adjustments.
- Treating policy as code allows version control, testing, and automation, while policy as data supports fine-grained, user-defined access controls.
- Organizations adopting dynamic authorization benefit from reduced operational costs, improved agility, enhanced security, and better customer experiences.
- Businesses can use dynamic authorization as a competitive advantage, enabling new product capabilities, faster compliance adaptation, and stronger security.
- Authorization is a strategic investment, not just a security measure—organizations that adopt policy-based access control gain efficiency, scalability, and security.
 Dynamic Authorization ebook for free
Dynamic Authorization ebook for free