5 ISC2 Code of Ethics
This chapter explains why a strong ethical foundation is indispensable for cybersecurity professionals who are entrusted with sensitive data, privileged access, and powerful tools. It distinguishes personal ethics from professional ethics and shows how formal codes guide behavior when competing values collide. Through common dilemmas—such as balancing compassion and fairness, privacy and transparency, or safety and profit—the chapter frames ethics as practical decision-making anchored in policies, law, and professional standards.
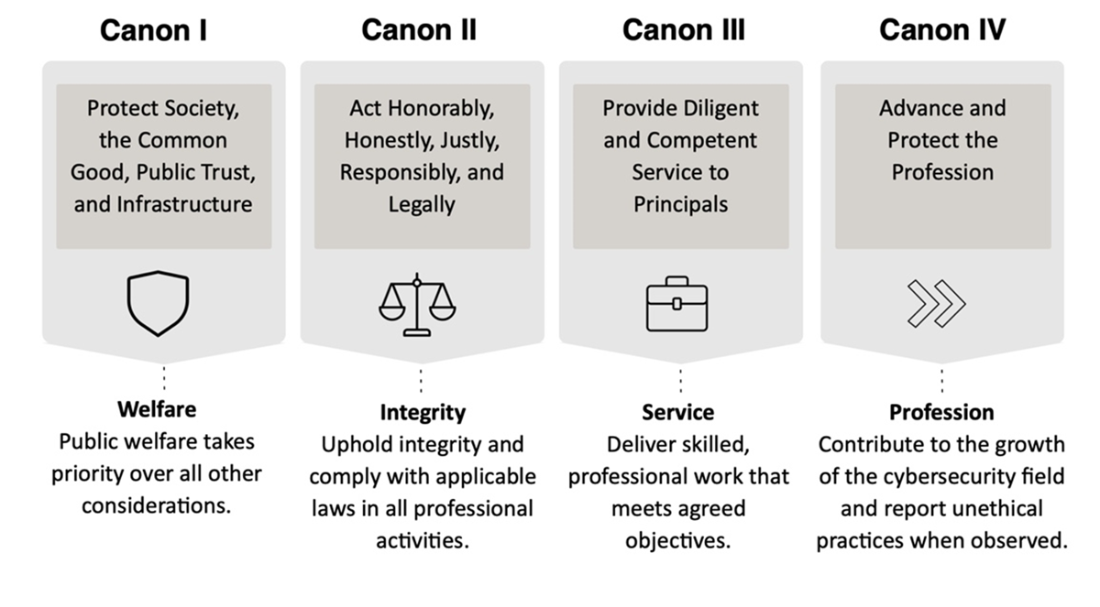
ISC2’s Code of Ethics is presented as the profession’s compass, composed of a preamble and four canons that set expectations for certified members. The preamble emphasizes safeguarding society and the common good and makes compliance a condition of certification. The four canons require practitioners to: prioritize societal welfare and public trust, including the security of critical infrastructure; act honorably, honestly, responsibly, and within the law; deliver competent, diligent, and economical service to their principals; and advance and protect the profession through continuous learning, community contribution, and addressing unethical conduct.
Practical guidance illustrates how intent, impact, and legality determine ethical standing in day-to-day choices (for example, the acceptable use of public information, or the risks of deceptive online personas). The chapter also outlines reporting: anyone may file complaints related to the first two canons, canon III complaints require a contractual relationship, and canon IV matters are limited to ISC2 members. Candidates must sign the Code after passing the exam, and the exam may test scenario-based judgment. Ultimately, consistent adherence to these standards builds trust, safeguards organizations and the public, and underpins professional credibility.
Summary of ISC2 Canons and their main goals
Answers to Review Questions
- The correct answer is B. While reporting security vulnerabilities is an important aspect of information security; it is not explicitly stated as a principle within the ISC2 Code of Ethics Canons.
- The correct answer is C. Provide diligent and competent service to principals. This principle emphasizes the importance of providing quality service to clients or employers and fulfilling professional responsibilities with due care and expertise.
- The correct answer is A. Protect society, the common good, necessary public trust and confidence, and the infrastructure. This Canon emphasizes a security analyst's duty to avoid harm and uphold public well-being by protecting society, the common good, necessary public trust and confidence, and the infrastructure.
- The correct answer is D. Having fake social media profiles and accounts can be socially objectionable but does not violate the ISC2 Ethics Canons. That being said, seeking to gain unauthorized access to resources on the internet, compromising the privacy of users, and disrupting the intended use of the internet are all considered unethical behaviors by ISC2, as well as by other similar professional organizations. Aside from being violations of professional codes of conduct, such actions may also be in violation of laws and regulations.
- The correct answer is C. The ISC2 Code of Ethics applies specifically to ISC2 members and certified professionals, not to all members of the information security. All the other statements are true. Adherence to the code is a condition of certification, failure to comply with the code may result in revocation of certification, and members who observe a breach of the code are required to report the possible violation.
FAQ
What is the ISC2 Code of Ethics and why does it matter for CC candidates?
The Code sets professional standards for integrity, accountability, and respect for the law and stakeholders. Adherence is a condition of certification, and all Certified in Cybersecurity (CC) candidates must sign it after passing the exam.What does the Preamble emphasize?
It stresses a duty to protect society and the common good, maintain public trust, and serve clients and peers ethically. It also states that strict adherence to the Code is mandatory for certification.What are the four ISC2 Code of Ethics canons?
- Protect society, the common good, public trust and confidence, and the infrastructure: Put public welfare and trust first and safeguard digital infrastructure.- Act honorably, honestly, justly, responsibly, and legally: Demonstrate integrity, avoid improper favors, consider consequences, and obey the law.
- Provide diligent and competent service to principals: Deliver skilled, accurate, relevant, and efficient work to those who engage your services.
- Advance and protect the profession: Pursue continuing education, contribute to the community, and report unethical conduct.
 Become ISC2 Certified in Cybersecurity ebook for free
Become ISC2 Certified in Cybersecurity ebook for free